cybersecurity attack vectors
Worldwide Cybersecurity Laws, Regulations, Directives, Standards. 9 Pics about Worldwide Cybersecurity Laws, Regulations, Directives, Standards : Download Protect Against Cyber Attacks Infographic for free in 2020, Cyber Security Incidents | Detection & Attack Vectors of Cyber Security and also AI Brings a New Pace in Cyber Security - Kratikal Blogs.
Worldwide Cybersecurity Laws, Regulations, Directives, Standards
 blog.radware.com
blog.radware.com
regulations laws standards directives cyber cybersecurity security
What Is An Ethical Hacker And What Does The Work Entail?
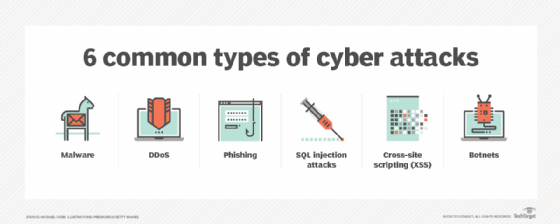 searchsecurity.techtarget.com
searchsecurity.techtarget.com
ethical hacker cybersecurity threats
Download Protect Against Cyber Attacks Infographic For Free In 2020
 www.pinterest.com
www.pinterest.com
cyber attacks protect informatici attacchi dagli proteggere infografica cyberaanvallen bescherm tegen cybersecurity cyberangriffen threats cybrary gratuito
How To Ensure Automotive Cybersecurity In The Next-Gen Vehicles [Part 1
 www.infopulse.com
www.infopulse.com
cybersecurity infopulse
Attack Surface Analysis – SwordSec
 swordsec.com
swordsec.com
Risk Mitigation Consulting, Inc. - Cybersecurity
 riskmitigationconsulting.com
riskmitigationconsulting.com
cyber risk expertise mitigation cybersecurity techniques management strategies
What The Heck Is A Watering Hole Attack? - WyzGuys Cybersecurity
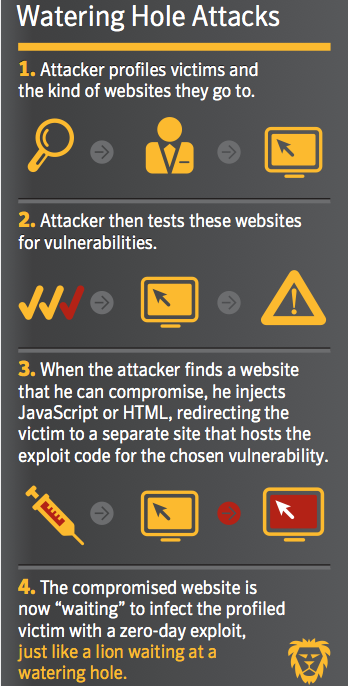 wyzguyscybersecurity.com
wyzguyscybersecurity.com
hole watering attack heck water cybersecurity wyzguys wyzguyscybersecurity
AI Brings A New Pace In Cyber Security - Kratikal Blogs
 www.kratikal.com
www.kratikal.com
intelligence cybersecurity defense menggunakan kratikal bijak mencegah invent leveraging artificially
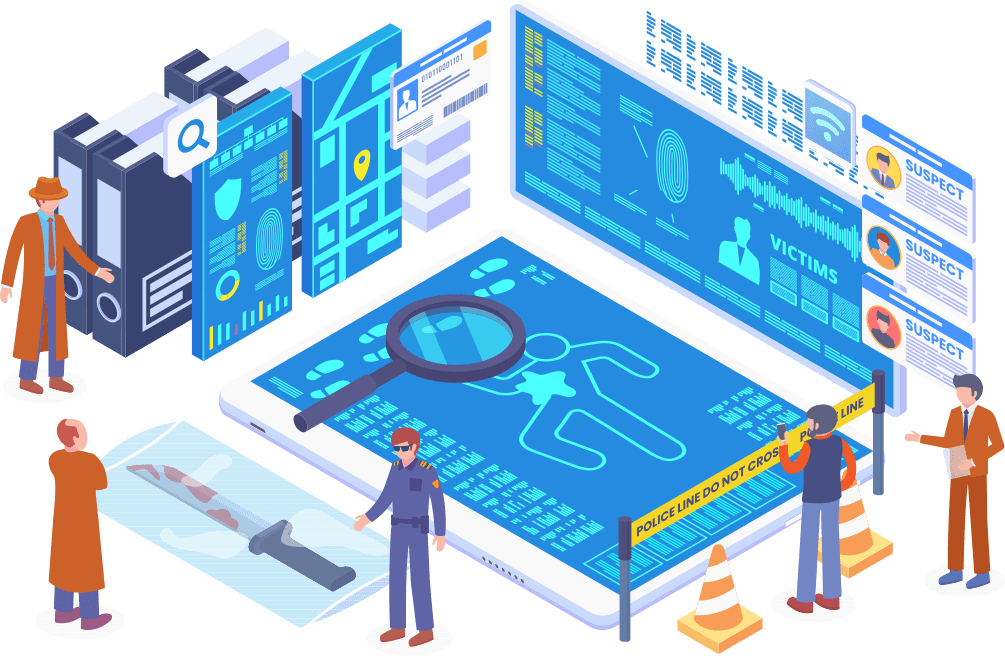
Cyber Security Incidents | Detection & Attack Vectors Of Cyber Security
 www.educba.com
www.educba.com
incidents
What is an ethical hacker and what does the work entail?. Ethical hacker cybersecurity threats. What the heck is a watering hole attack?